“Ignoring AI now means the United States will lag behind more forward-thinking countries that invest in AI today. While the United States waits “50 to 100 years” for AI to become a reality of life, other countries will be doing the hard work, laying the necessary infrastructure, and gaining from machine learning, and the human learning that goes along with it.”
Category Archives: Computers
This Picture Will Change the Way You Learn to Code – Saul Costa – Medium
As a developer, there is too much out there to master everything. Don’t even try. Learn how you work best as a developer, build a toolset that fits you, and don’t try to have all the answers. Focus on learning how to find the answers quickly.
Source: This Picture Will Change the Way You Learn to Code – Saul Costa – Medium
5 Neuroscience Experts Weigh in on Elon Musk’s Mysterious “Neural Lace” Company – IEEE Spectrum
What can we expect from Neuralink, the new Elon Musk company devoted to brain-computer interfaces?
This is very exciting technology, and I am fascinated by what it could mean. Here Eliza Strickland asks 5 neuroscience types what they implications and limitations could be.
Source: 5 Neuroscience Experts Weigh in on Elon Musk’s Mysterious “Neural Lace” Company – IEEE Spectrum
Database Breaches Still Plague the Internet, But There’s Hope Ahead | WIRED
While companies commonly use these databases to store tempting troves of customer and financial data, they often do so with outdated and weak default security configurations. And while any type of database can be left open or unprotected, a string of breaches over the last few years have all centered around one type in particular: open-source “NoSQL” databases, particularly those using the popular MongoDB database program.
Source: Database Breaches Still Plague the Internet, But There’s Hope Ahead | WIRED
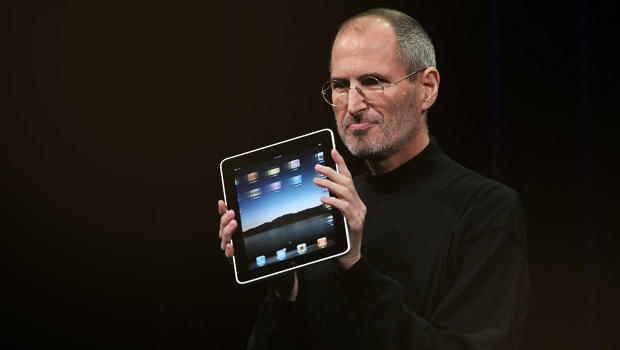
Apple Sucks Now, Here’s A ThinkPad Buyer’s Guide
” A MacBook is a business-class laptop, and of course carries a higher price tag. However, Apple’s latest hardware release was underwhelming and overpriced. If you’re looking for a new laptop, you would do well to consider other brands. To that end, here’s a buyer’s guide to ThinkPads, currently the second most popular laptop I’ve seen with the dev/hacker/code cracker crowd.”
UVA Computer Science Professor Applies Genetic Engineering Principles to Cybersecurity | UVA Today
Double Helix is based on concept called structured diversity. It creates a number of functionally equivalent versions of a mission-critical system, but adjusts the binary code of some of these clones – the equivalent to changing their four-letter DNA code – so that properties needed for successful attacks are missing. When a cyberattack occurs, the behavior of the unprotected clones diverges from the protected ones. At this point, Double Helix will take action to recover from the attack by modifying the affected clones.
Source: UVA Computer Science Professor Applies Genetic Engineering Principles to Cybersecurity | UVA Today
The Extraordinary Link Between Deep Neural Networks and the Nature of the Universe
Artificial neural networks are famously based on biological ones. So not only do Lin and Tegmark’s ideas explain why deep learning machines work so well, they also explain why human brains can make sense of the universe. Evolution has somehow settled on a brain structure that is ideally suited to teasing apart the complexity of the universe.
This work opens the way for significant progress in artificial intelligence. Now that we finally understand why deep neural networks work so well, mathematicians can get to work exploring the specific mathematical properties that allow them to perform so well. “Strengthening the analytic understanding of deep learning may suggest ways of improving it,” say Lin and Tegmark.
Deep learning has taken giant strides in recent years. With this improved understanding, the rate of advancement is bound to accelerate.
Source: The Extraordinary Link Between Deep Neural Networks and the Nature of the Universe
Meet PocketBlock, the crypto engineering game for kids of all ages
When you’re a cryptographer, telling your preteen kids what you do isn’t easy.
“While suitable for kids eight and older, PocketBlock is by no means restricted to kids. Troutman said it’s also suitable for professional developers who want to deepen their understanding of the way cryptographic algorithms work, given that they’re often implementing them.”
Source: Meet PocketBlock, the crypto engineering game for kids of all ages
Quantum Computing Just Grew Way the Hell Up
“On Wednesday, researchers at the Joint Quantum Institute at the University of Maryland unveiled a first-of-its-kind fully programmable and reconfigurable quantum computer. The five-qubit machine, which is described in the journal Nature, represents a dramatic step toward general-purpose quantum computing—and, with it, an upending of what we can even consider to be computable.”
Be Prepared: We’re Entering A Post-Device Era
“[…] the future of computing seems to be about a set of platform and device-independent services. Specifically, voice-based interactions, driven by large installations of cloud-based servers running deep learning-based algorithms are what’s hot these days. This kind of computing model doesn’t necessarily need the kind of local horsepower that traditional computing devices have had. Indeed, these types of services can be accessed by the simplest of devices, with little more than an audio input, an audio output, and a wireless connection.”